Apache 2
Contents
- 1 Requirements
- 2 Installation
- 3 PHP 5
- 4 Apache 2 configuration # Multi-threading
- 5 Apache 2 configuration # Virtual host
- 6 Apache 2 configuration # SSL Virtual host
- 7 Apache 2 configuration # Redirect HTTP to HTTPS
- 8 Apache 2 # redirections using mod_proxy
- 9 Apache 2 configuration # LDAP authentication
- 10 Apache 2 configuration # Advanced configuration
- 11 Apache 2 and PHP5: Secure your installation!
- 12 Apache2 configuration # Improve server performances
Requirements
Before going through this tutorial, I recommend you to setup:
- MySQL server
- SSL infrastructure and create a server certificate - see SSL server
- LDAP server
Installation
Apache 2
This will install web server + PHP + Perl + all required libraries.
Apache2 core
apt-get install apache2 apache2-mpm-prefork apache2-utils ssl-certAdditional libraries
apt-get install libapache2-mod-fcgid librubyDoc
apt-get install apache2-docPerl
apt-get install libapache2-mod-perl2 libapache2-mod-perl2-docPHP 5
Core
apt-get install libapache2-mod-php5 php5 php5-commonModule PHP5
apt-get install php5-curl php5-dev php5-gd php-pear php5-imagick php5-imap php5-mcrypt
apt-get install php5-memcache php5-mhash php5-mysql php5-snmp php5-xmlrpc php5-xcache php5-curl php5-xslAdditional libs
apt-get install php5-cli php5-cgi php-pear php-auth php5-mcrypt mcryptImage Magick
apt-get install php5-imagick imagemagick
Firewall
You have to open the following ports:
- Port 80 = HTTP
- Port 443 = HTTPS
$IPTABLES -A INPUT -p tcp -m state -i eth0 --dport 80 -j ACCEPT
$IPTABLES -A INPUT -p tcp -m state -i eth0 --dport 443 -j ACCEPTRestart the firewall
/etc/init.d/firewall restart
PHP 5
Edit config file:
vim /etc/php5/apache2/php.iniAdd / uncomment the following lines in Dynamic extensions area (~ line 865)
- extension=mysql.so
- extension=gd.so
Apache 2 configuration # Multi-threading
MPM prefork
This manage processes
- Max clients = nb of max simultaneous requests that the server can handle
- Server limit = max nb of process that the server can handle
- Start servers = nb of process to create on server start
- Min / Max spare servers = nb of min / max process listening for incoming request
- Max request per child = nb of requests that each process can execute
vim /etc/apache2/apache2.confLet default values; put a limit to MaxRequestsPerChild at 100 000
MPM worker
This manage threads. Threads are executed within a specific process. All process’ threads share the same context and global variables.
vim /etc/apache2/apache2.confLet default values; put a limit to MaxRequestsPerChild at 10 000
Apache 2 configuration # Virtual host
Preparation
Initialize configuration
cd /etc/apache2/sites-available/Create target directory
mkdir -p /var/www/myServerPrepare the log files
mkdir -p /var/log/apache2/myServer
touch /var/log/apache2/myServer/access.log
touch /var/log/apache2/myServer/error.log
chmod -R 660 /var/log/apache2/myServer/*
chown -R www-data:www-data /var/log/apache2/myServer/*
Configuration
Init configuration
cp /etc/apache2/sites-available/000-default.conf /etc/apache2/sites-available/myServer.conf
Edit configuration
vim /etc/apache2/sites-available/myServer
To begin the virtual host, write the following lines:
→ Adjust the settings to your own configuration
<VirtualHost 192.168.0.100:80> → Choose the best options for your needs
<VirtualHost *:80>
ServerName myServer
ServerAlias www.myServer *.myServer
ServerAdmin webmaster@domain
# Logs settings
LogLevel Warn
CustomLog {APACHE_LOG_DIR}/myServer/access.log combined
ErrorLog {APACHE_LOG_DIR}/myServer/error.log
# Root folder properties
DocumentRoot /var/www/myServer
<Directory />
Options FollowSymLinks
AllowOverride None
</Directory>
<Directory /var/www/myServer />
Options Indexes FollowSymLinks MultiViews
AllowOverride None
Order allow,deny
allow from all
</Directory>
# Scripts CGI
# [ required for PHP 5 ]
ScriptAlias /cgi-bin/ /var/www/cgi-bin
<Directory "/var/www/cgi-bin">
AllowOverride None
Options +ExecCGI -MultiViews +SymLinksIfOwnerMatch
Order allow,deny
Allow from all
</Directory>
</VirtualHost>
Activation of a Virtual Host
To activate a Virtual Host, just type
a2ensite myServerThen, restart your web server
/etc/init.d/apache2 restartApache 2 configuration # SSL Virtual host
Create SSL certificate
First of all, you need to create a server certificate. Cf. SSL dedicated document → Create a new server certificate
>> see SSL server
Enable SSL module
Create symlinks for server certificate
ln -s /srv/ssl/certs/myServer.cert.pem /etc/apache2/webServer.pem
ln -s /srv/ssl/private/myServer.nopass.key /etc/apache2/webServer.key
Activate the SSL module
a2enmod ssl
Prepare virtual host (optional)
Create virtual host folder
mkdir -p /var/www/myServer-ssl
cp /var/www/index.html /var/www/myServer-ssl
chown -R www-data:www-data /var/www/myServer-ssl
Prepare the log files (optional)
mkdir -p /var/log/apache2/myServer-ssl
touch /var/log/apache2/myServer-ssl/error.log
touch /var/log/apache2/myServer-ssl/access.log
chmod 660 /var/log/apache2/*
chown root:www-data /var/log/apache2/*
Virtual host declaration
You have 2 possibilities:
- Update your current virtual host
- Create a new one, only for the SSL virtual host
New virtual host: Init configuration
cp /etc/apache2/sites-available/default-ssl /etc/apache2/sites-available/myServer-ssl
Edit V.Host configuration
vim /etc/apache2/sites-available/myServer-ssl
Then, you will need to edit the Virtual Host configuration file:
vim /etc/apache2/sites-availables/virtualHostName!! Adjust the settings to your own configuration
# Secure web server
<VirtualHost _default_:443>
<VirtualHost 192.168.0.100:443> → Choose the best options for your needs
<VirtualHost *:443>
ServerName myServer
ServerAlias www.myServer *.myServer
ServerAdmin webmaster@domain
# Logs settings
LogLevel Warn
CustomLog {APACHE_LOG_DIR}/myServer-ssl/access.log combined
ErrorLog {APACHE_LOG_DIR}/myServer-ssl/error.log
# Root folder properties
DocumentRoot /var/www/myServer-ssl
# Enable SSL
SSLEngine On
SSLCertificateFile /etc/apache2/webServer.pem
SSLCertificateKeyFile /etc/apache2/webServer.key
# Root directory properties
<Directory /var/www/ssl />
Options Indexes FollowSymLinks MultiViews
AllowOverride None
Order allow,deny
allow from all
</Directory>
##########################
# ALIAS AND REDIRECTIONS #
##########################
</VirtualHost>Enable site
a2ensite myServer-sslRestart the web server
/etc/init.d/apache2 restartAccept auto-signed certificate
Go to https://myServer/certs/ Cf SSL document to get installation details
Apache 2 configuration # Redirect HTTP to HTTPS
The safer way to redirect HTTP to HTTPS is use to adjust the virtual host configuration.
Edit configuration
vim /etc/apache2/sites-available/myServerMake it looks like:
<VirtualHost *:80>
ServerAdmin guillaume@qin-diaz.com
ServerName dev.daxiongmao.eu
ServerAlias *.dev.daxiongmao.eu dev.qin-diaz.com www.dev.qin-diaz.com
### LOG ###
ErrorLog ${APACHE_LOG_DIR}/daxiongmao/error.log
LogLevel warn
CustomLog ${APACHE_LOG_DIR}/daxiongmao/access.log combined
## Redirect all traffic to HTTPS website
redirect permanent / https://myServer/
## No need of a document root anymore as everything is redirect
</VirtualHost>You can remove:
- Document root
- CGI url
- All the alias
Restart your server
service apache2 restart
Apache 2 # redirections using mod_proxy
Thanks to Julien Rialland for his insight regarding this part!
Principle
The proxy module allow you to redirect remote user to a specific server that can be host on a different machine or port through a clear URL.
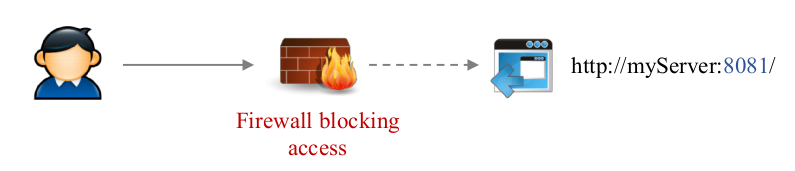
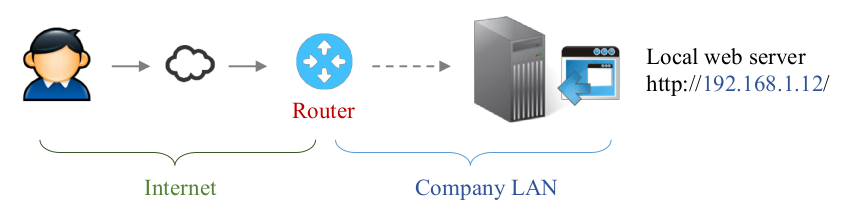
Current limits
Some application are not available from outside…
- For security reasons [default URL is not allowed]
- Due to network issues
Proxy module role
The proxy module allow you to provide access through transparent redirection.
It relies on:
- Already open port (80 or 443)
- Redirection rule
- Each service URL must be unique
- The target service must be reachable by the web server
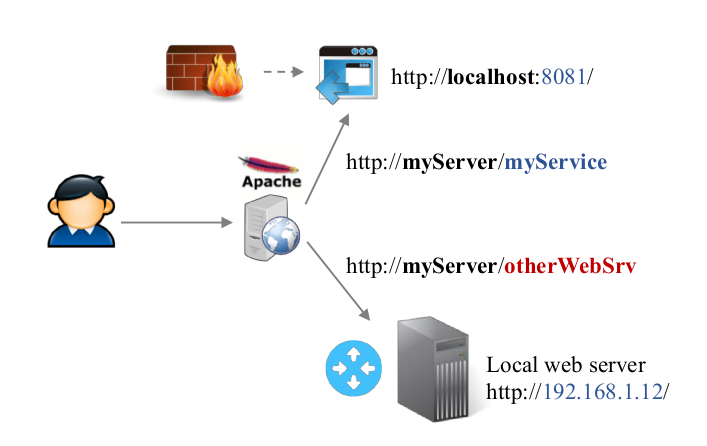
As you can see on the following example, the previous services will be accessible using some dedicated URL.
Remote “http://myServer/myService” will redirect to “http://localhost:8081”
→ The mod_proxy is none intrusive. You don’t have to change anything is the orginal service configuration. Apache2 will handle all the transformations.
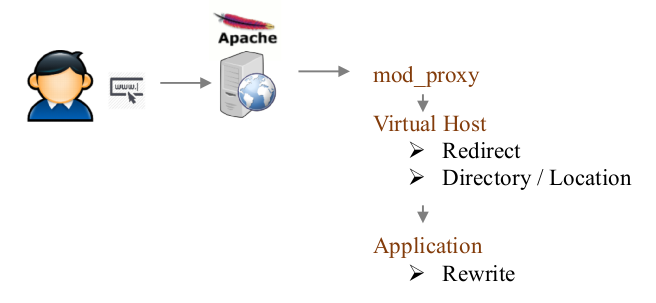
Proxy / redirect / rewrite
When Apache2 receive a request it will be process in the following order:
So, even if you enable a full redirection to HTTPS you can still use some HTTP service through mod_proxy.
Enable proxy module
a2enmod proxy proxy_http proxy_ajpConfigure proxy redirections
You have to edit / create the configuration file.
vim /etc/apache2/mods-enabled/proxy.confAdjust the file to:
<IfModule mod_proxy.c>
#ProxyRequests On # Do NOT enable this
# Allow proxy for all incoming requests and users
<Proxy *>
AddDefaultCharset off
Order deny,allow
Allow from all
Satisfy any
</Proxy>
# Enable the handling of HTTP/1.1 "Via:" headers.
ProxyVia On
# Keep current server name in URL
ProxyPreserveHost On
# ---------------------
# Some proxy examples
# ---------------------
# Service JIRA is on another computer, if local network
ProxyPass /jira http://192.168.1.12:8080/jira
ProxyPassReverse /jira http://192.168.1.12:8080/jira
# Service ARTIFACTORY runs on a different port
ProxyPass /artifactory http://localhost:8081/artifactory
ProxyPassReverse /artifactory http://localhost:8081/artifactory
</IfModule>Some notes:
- Do NOT put a / after the target URL
- Do NOT use / as ProxyPass source, use the previous redirect permanent instead
Apply changes and test result
service apache2 restartNavigate to http://myServer/artifactory
Apache 2 configuration # LDAP authentication
Enable LDAP module
a2enmod authnz_ldap
service apache2 restart
Configuration
You can use the following settings inside a “.htaccess” or “VirtualHost” configuration:
Edit configuration
vim /etc/apache2/sites-available/myServerAdjust your virtual-host like that:
# LDAP protected directory
<Directory /var/www/ssl/secure>
Options Indexes FollowSymLinks MultiViews
AllowOverride None
Order allow,deny
allow from all
AuthType basic
AuthName "Secure area"
AuthBasicProvider ldap
AuthLDAPUrl "ldap://localhost:389/{LDAP ou=,dc=}?uid"
Require valid-user
# example
# AuthLDAPBindDN "cn=admin,dc=dev,dc=daxiongmao,dc=eu"
# AuthLDAPUrl "ldap://localhost:389/ou=people,dc=dev,dc=daxiongmao,dc=eu?uid"
</Directory>
Secure all the website
You have to adjust you document root like that:
<VirtualHost _default_:443>
# Restrict access to document root
DocumentRoot /var/www/daxiongmao-ssl
<Directory />
Options FollowSymLinks
AllowOverride None
Order allow,deny
deny from all
</Directory>
<Directory /var/www/daxiongmao-ssl>
Options Indexes FollowSymLinks MultiViews
AllowOverride None
Order allow,deny
allow from all
AuthType basic
AuthName "Secure area"
AuthBasicProvider ldap
AuthLDAPUrl "ldap://localhost:389/ou=people,dc=dev,dc=daxiongmao,dc=eu?uid"
Require valid-user
</Directory>
[…]
Apache 2 configuration # Advanced configuration
Enable redirections
Mod rewrite allows you to redirect source URL to another one.
Enable module
a2enmod rewrite
Alias redirection
Edit configuration
vim /etc/apache2/sites-available/myServerHTTP virtual host = redirect to HTTPS
<VirtualHost *:80>
RewriteRule ^/myAlias(/.*|$) https://%{HTTP_HOST}/myAlias$1 [L,R]
<Location /myAlias >
order deny,allow
deny from all
# Only allow specific IP@
# allow from 127.0.0.1 192.168.0.0/255.255.255.0
allow from all
</Location>
</VirtualHost>HTTPS virtual host = service declaration
<VirtualHost _default_:443>
# PHPSecInfo
Alias /myAlias /var/www/myAlias
<Location /myAlias >
order deny,allow
deny from all
# Only allow specific IP@
# allow from 127.0.0.1 192.168.0.0/255.255.255.0
allow from all
</Location>
</VirtualHost>Reload your configuration
/etc/init.d/apache2 reload
Redirect HTTP to HTTPS
This is not the recommended method. You should use the previous method instead.
<VirtualHost *:80>
ServerAdmin guillaume@qin-diaz.com
ServerName dev.daxiongmao.eu
ServerAlias *.dev.daxiongmao.eu dev.qin-diaz.com www.dev.qin-diaz.com
### LOG ###
ErrorLog ${APACHE_LOG_DIR}/daxiongmao/error.log
LogLevel warn
CustomLog ${APACHE_LOG_DIR}/daxiongmao/access.log combined
## Redirect all traffic to HTTPS website
RewriteEngine On
# This checks to make sure the connection is not already HTTPS
RewriteCond %{HTTPS} !=on
# This rule will redirect users from their original location,
# to the same location but using HTTPS.
RewriteRule ^/?(.*) https://%{SERVER_NAME}/$1 [R,L]
## No need of a document root anymore as everything is redirect
</VirtualHost>
Module configuration
Create the module configuration file
vim /etc/apache2/conf.d/rewrite.confCopy / paste this configuration (adjust to your own settings!)
RewriteEngine On
# --------------------- SECURITY RULES (JOOMLA) ------------------------ #
## End of deny access to extension xml files
RewriteCond %{QUERY_STRING} mosConfig_[a-zA-Z_]{1,21}(=|\%3D) [OR]
# Block out any script trying to base64_encode crap to send via URL
RewriteCond %{QUERY_STRING} base64_encode.*\(.*\) [OR]
# Block out any script that includes a <script> tag in URL
RewriteCond %{QUERY_STRING} (\<|%3C).*script.*(\>|%3E) [NC,OR]
# Block out any script trying to set a PHP GLOBALS variable via URL
RewriteCond %{QUERY_STRING} GLOBALS(=|\[|\%[0-9A-Z]{0,2}) [OR]
# Block out any script trying to modify a _REQUEST variable via URL
RewriteCond %{QUERY_STRING} _REQUEST(=|\[|\%[0-9A-Z]{0,2})
# Send all blocked request to homepage with 403 Forbidden error!
RewriteRule ^(.*)$ index.php [F,L]
# --------------------- SECURITY RULES (PERSONAL) ------------------------ #
## DENY REQUEST BASED ON REQUEST METHOD ###
RewriteCond %{REQUEST_METHOD} ^(TRACE|TRACK|OPTIONS|HEAD)$ [NC]
RewriteCond %{REQUEST_METHOD} (GET|POST) [NC]
RewriteRule ^.*$ - [F]
# Eviter les failles de securite
RewriteCond %{QUERY_STRING} ^(.*)http(\:|\%3A)(.*)$
RewriteCond %{QUERY_STRING} mosConfig_ [NC,OR]
RewriteCond %{QUERY_STRING} ^(.*)(%3C|<)/?script(.*)$ [NC,OR]
RewriteCond %{QUERY_STRING} ^(.*)(%3D|=)?javascript(%3A|:)(.*)$ [NC,OR]
RewriteCond %{QUERY_STRING} ^(.*)document\.location\.href(.*)$ [NC,OR]
RewriteCond %{QUERY_STRING} ^(.*)base64_encode(.*)$ [NC,OR]
RewriteCond %{QUERY_STRING} ^(.*)GLOBALS(=|[|%[0-9A-Z]{0,2})(.*)$ [NC,OR]
RewriteCond %{QUERY_STRING} ^(.*)_REQUEST(=|[|%[0-9A-Z]{0,2})(.*)$ [NC,OR]
RewriteCond %{QUERY_STRING} ^(.*)(SELECT|INSERT|DELETE|CHAR\(|UPDATE|REPLACE|LIMIT)(.*)$
# Eviter les erreurs basiques
RewriteCond %{QUERY_STRING} \.\.\/ [NC,OR]
RewriteCond %{QUERY_STRING} boot\.ini [NC,OR]
RewriteCond %{QUERY_STRING} tag\= [NC,OR]
RewriteCond %{QUERY_STRING} ftp\: [NC,OR]
RewriteCond %{QUERY_STRING} http\: [NC,OR]
RewriteCond %{QUERY_STRING} https\: [NC,OR]
RewriteCond %{QUERY_STRING} mosConfig [NC,OR]
RewriteCond %{QUERY_STRING} ^.*(\(|\)|<|>|'|"|\?|\*).* [NC,OR]
RewriteCond %{QUERY_STRING} ^.*(%22|%27|%3C|%3D|%3E|%7B|%7C).* [NC,OR]
RewriteCond %{QUERY_STRING} ^.*(%0|%A|%B|%C|%D|%F|127\.0).* [NC,OR]
RewriteCond %{QUERY_STRING} ^.*(globals|encode|localhost|loopback).* [NC,OR]
RewriteCond %{QUERY_STRING} ^.*(select|insert|union|declare|drop).* [NC]
RewriteRule ^(.*)$ - [F,L]
# Ban Typical Vulnerability Scanners and others
# Kick out Script Kiddies
RewriteCond %{HTTP_USER_AGENT} ^(java|curl|wget).* [NC,OR]
RewriteCond %{HTTP_USER_AGENT} ^.*(libwww-perl|curl|wget|python|nikto|wkito|pikto|scan|acunetix).* [NC,OR]
RewriteCond %{HTTP_USER_AGENT} ^.*(winhttp|HTTrack|clshttp|archiver|loader|email|harvest|extract|grab|miner).* [NC,OR]
# Eviter les programmes de Zombies
RewriteCond %{HTTP_USER_AGENT} ^Anarchie [OR]
RewriteCond %{HTTP_USER_AGENT} ^ASPSeek [OR]
RewriteCond %{HTTP_USER_AGENT} ^attach [OR]
RewriteCond %{HTTP_USER_AGENT} ^autoemailspider [OR]
RewriteCond %{HTTP_USER_AGENT} ^Xaldon\ WebSpider [OR]
RewriteCond %{HTTP_USER_AGENT} ^Xenu [OR]
RewriteCond %{HTTP_USER_AGENT} ^Zeus.*Webster [OR]
RewriteCond %{HTTP_USER_AGENT} ^Zeus
RewriteRule ^.* - [F,L]
# Allow the robots to reference our website
RewriteCond %{HTTP_USER_AGENT} !^Googlebot [NC]
RewriteCond %{HTTP_USER_AGENT} !^Googlebot-Image [NC]
RewriteCond %{HTTP_USER_AGENT} !^Googlebot-Mobile [NC]
RewriteCond %{HTTP_USER_AGENT} !^Msnbot [NC]
RewriteCond %{HTTP_USER_AGENT} !^Mediapartners-Google [NC]
# Keep request without referer
RewriteCond %{HTTP_REFERER} !^$
# To allow your pictures to be displayed on Google
RewriteCond %{HTTP_REFERER} !^http://.*google\.(comŠ(co\.)?[a-z]{2})/
# To forbid the copy of your pictures to anyone else : display an other image !
RewriteRule .*\.(jpe?g|gif|bmp|png)$ /images/hotlinkis.jpg [L]
Take changes into account
You have to restart the server to use this settings
service apache2 restart
Ports number
You can change the Apache2 server ports
vim /etc/apache2/ports.confEdit
# HTTP
Listen 80
# HTTPS
Listen 443
Restricted access
Edit configuration
vim /etc/apache2/sites-available/myServerIf your server is directly accessible on Internet: you should protect it!
# Disable access to the entire file system except for the directories that
# are explicitly allowed later.
#
<Directory />
AllowOverride None
Order Deny,Allow
Deny from all
</Directory>
# Protect .htacess files
<Files ~ "^\.ht">
Order allow,deny
Deny from all
</Files>
Be discreet!
Check the current server status using a simple PHP info file
Do not gives details about your configuration to outsiders.
vim /etc/apache2/conf.d/securitySet the following settings
#### Ask your server to be more discret!
# ServerTokens
# Set to one of: Full | OS | Minimal | Minor | Major | Prod
ServerTokens Prod
ServerSignature Off
TraceEnable OffRestart Apache2
service apache2 restartRe-run PHP info, you should have less information.
Apache 2 and PHP5: Secure your installation!
PHP Security Info
If you want to test your PHP security, you can use the PHPSecInfo tool, available at: http://phpsec.org/projects/phpsecinfo/index.html
Installation
cd /tmp
wget http://phpsec.org/projects/phpsecinfo/phpsecinfo.zip
unzip phpsecinfo.zip
mv phpsecinfo-Version phpsecinfo
mv phpsecinfo/ /var/www
cd /var/www
chown -R www-data:www-data phpsecinfo
Virtual host configuration
Edit configuration
vim /etc/apache2/sites-available/myServer!! For security reason: DO NOT use 'phpsecinfo' as alias. It's too easy to guess.
<VirtualHost *:80>
# Advanced redirection – Only allow specific IP @
RewriteRule ^/phpsec(/.*|$) https://%{HTTP_HOST}/phpsec$1 [L,R]
<Location /phpsec >
order deny,allow
deny from all
# Only allow specific IP@
# allow from 127.0.0.1 192.168.0.0/255.255.255.0
allow from all
</Location>
</VirtualHost>
<VirtualHost _default_:443>
# PHPSecInfo
Alias /phpsec /var/www/phpsecinfo
<Location /phpsec >
order deny,allow
deny from all
# Only allow specific IP@
# allow from 127.0.0.1 192.168.0.0/255.255.255.0
allow from all
</Location>
</VirtualHost>Reload your configuration
/etc/init.d/apache2 reload
Run the test
To asset your current installation you can run the test: https:// myServer/phpsec
Improve security
PHP5 sessions and temp files
Create specific directory to store the sessions and temp files:
mkdir -p /etc/php5/temp
mkdir -p /etc/php5/session
chown -R www-data:root /etc/php5/temp
chown -R www-data:root /etc/php5/session
chmod -R 770 /etc/php5/session
chmod -R 770 /etc/php5/tempEdit the configuration file
vim /etc/php5/apache2/php.iniline 798 → upload_tmp_dir = /etc/php5/temp line 1409 → session.save_path = "/etc/php5/session"
PHP5 tweak
vim /etc/php5/apache2/php.iniline 261 → expose_php = Off line 480 → display_errors=Off line 675 → post_max_size=256K line 814 → allow_url_fopen=Off
DO NOT enable the open_basedir (even if the test say so! It’s a troublesome setting)
Restart your server to load the changes:
service apache2 restartRe-run the test. Then:
- Ignore the open_basedir and upload_tmp_dir alerts, if any.
- You can enable some specific options with a .htaccess file
Change Apache 2 UID
Do not change the UID if you already have install web programs such as phpldapadmin or phpmyadmin, cacti, ...
Change the Apache UID
vim /etc/groupChange www-data UID
www-data:x:10033:Change the Apache GID
vim /etc/passwdChange the group settings
www-data:x:10033:10033:www-data:/var/www:/bin/falseApply modifications
chown -R www-data:www-data /var/www/*
chown -R www-data:root /etc/php5/*To take on the modifications you have to reboot your server.
Avoid DOS attacks
Source: Linux mag’ – Hors serie Apache2
You can protect your server from Denial Of Service (DOS) attacks through mod_evasive
apt-get install libapache2-mod-evasivePrepare log directory
mkdir /var/log/apache2/mod_evasive
chown -R www-data:www-data /var/log/apache2/mod_evasiveEnable module
a2enmod mod-evasive
Configuration
Create the configuration file
vim /etc/apache2/conf.d/mod_evasive.confPut:
# Mod evasive configuration
# Based upon Linux Mag
<IfModule mod_evasive20.c>
DOSHashTableSize 3097
# Limit user to 5 pages per 2 seconds
DOSPageCount 5
DOSPageInterval 2
# No more than 100 HTTP request per second (HTML, CSS, images, …)
DOSSiteCount 100
DOSSiteInterval 1
# Block client for 300 seconds
DOSBlockingPeriod 300
# Send alert email
#DOSEmailNotify "admin@myDomain"
# Log directory
DOSLogDir "/var/log/apache2/mod_evasive"
# Command to execute on ban
#DOSSystemCommand "/sbin/iptables -I INPUT -s %s -j DROP"
# Ignore following IP and networks
DOSWhiteList 127.0.0.1
#DOSWhitelist 66.249.65.*
<IfModule mod_evasive20.c>DosHashTableSize = Size of the hash table.
- The greater, the more memory is required but the faster it is! The value must be a prime number
Apply changes
service apache2 restart
Apache2 configuration # Improve server performances
Mod deflate: improved the bandwidth
To improve the bandwidth, you can compress pages and type of content.
=> You can improved your bandwidth from 20 to 30%.
To do so, you need a specific module for Apache: mod_deflate
a2enmod deflate
touch /var/log/apache2/deflate.log
chown www-data:www-data /var/log/apache2/deflate.log
chmod 740 /var/log/apache2/deflate.logEdit your web server configuration file:
vim /etc/apache2/conf.d/deflate.confAdd the following lines:
### Bandwidth optimization
<IfModule mod_deflate.c>
AddOutputFilterByType DEFLATE text/html text/plain text/xml text/javascript text/css application/x-javascript
DeflateFilterNote deflate_ratio
LogFormat "%v %h %l %u %t \"%r\" %>s %b"
CustomLog /var/log/apache2/deflate.log vhost_with_deflate_info
</IfModule>Restart your web server:
/etc/init.d/apache2 restart
Mod expires: use the cache of your clients
Another way to improve performances and bandwidth: use the client's cache.
To do so, you need a specific module for Apache: mod_expires
a2enmod expiresEdit your web server configuration file:
vim /etc/apache2/expires.confAdd the following lines
#### Client's cache settings
<IfModule mod_expires.c>
ExpiresActive on
# set the default to 24 hours
ExpiresDefault "access plus 24 hours"
# cache shockwave-flash for 2 weeks (days | weeks | mounths | years)
ExpiresByType application/x-shockwave-flash "access plus 2 weeks"
ExpiresByType flv-application/octet-stream "access plus 3 days"
# cache common graphics for 3 days
ExpiresByType image/jpg "access plus 2 weeks"
ExpiresByType image/gif "access plus 2 weeks"
ExpiresByType image/jpeg "access plus 2 weeks"
ExpiresByType image/png "access plus 2 weeks"
# cache CSS for 24 hours
ExpiresByType text/css "access plus 24 hours"
</IfModule>Restart your web server:
/etc/init.d/apache2 restart